EasyQuote Achieves Full CSP Compliance for Hyva Theme
EasyQuote is the first Magento 2 quote management extension to achieve full Content Security Policy (CSP) compliance on the Hyvä frontend theme. This means zero inline scripts, zero CSP violations, and full compatibility with strict CSP headers — critical for security-conscious B2B stores. The update also includes complete Hyvä Alpine.js component support and Tailwind CSS integration.
Content Security Policy implementation has become critical for Magento 2 stores following recent high-severity vulnerabilities. The CVE-2024-34102 "CosmicSting" vulnerability (CVSS 9.8) and CVE-2024-20720 demonstrated how cross-site scripting (XSS) attacks can compromise payment data and customer information. For platforms as complex as Magento, security vulnerabilities are inevitable - CSP provides essential defense-in-depth protection.
The timing coincides with significant news for the Magento ecosystem: Hyva Theme 1.4, including CSP functionality, became free and open-source in November 2025. Previously requiring a €1,000 license, this change removes the primary barrier to CSP adoption for thousands of merchants running Magento 2 storefronts.
format_list_bulleted Table of Contents
Why Hyva Theme Going Free Matters for Magento Security
The decision to make Hyva Theme free and open-source represents a watershed moment for Magento 2 security standardization. The €1,000 licensing cost was previously a significant adoption barrier, particularly for mid-market merchants and agencies managing multiple client stores.
Impact on the Ecosystem
CSP-ready architecture now available to all merchants, not just enterprise clients
Creates a unified security baseline across Hyva-powered stores
Drives third-party developers to prioritize CSP compatibility
Establishes CSP compliance as an expected standard, not a premium feature
New Hyva implementations start with CSP protection rather than requiring retrofitting
The availability of free CSP-compatible infrastructure means security is no longer a feature reserved for stores with large budgets. This democratization of protection mechanisms benefits the entire Magento community by raising baseline security standards across all implementation tiers.
Top 5 Reasons CSP Is Essential Today and in the Future
1. Strong Protection Against XSS Attacks
CSP blocks untrusted script execution at the browser level, preventing the most common attack vector in e-commerce platforms. By enforcing strict source allowlisting, CSP mitigates risks from compromised third-party scripts, malicious browser extensions, and injected code targeting payment flows or customer data.
Real-world context: The CosmicSting vulnerability (CVE-2024-34102) allowed arbitrary XML deserialization leading to remote code execution. While CSP cannot prevent server-side vulnerabilities, it provides critical client-side protection against the XSS components often used to exploit such vulnerabilities.
2. Long-Term Protection Against Future Vulnerabilities
CSP establishes a defensive layer that mitigates potential future exploits before they're discovered. When zero-day vulnerabilities emerge, CSP-protected stores have reduced attack surface while developers work on patches. This provides operational breathing room - critical security updates can be tested thoroughly rather than requiring emergency weekend deployments.
Operational benefit: Reduces mean time to remediation (MTTR) by containing threats while maintaining store availability.
3. Compliance with Modern Security Standards
Enterprise procurement and payment processing increasingly mandate client-side security controls. CSP directly supports:
- PCI DSS 4.0 - Requirement 6.4.3 specifically addresses script integrity and CSP implementation
- GDPR Article 32 - "Appropriate technical measures" for data protection include XSS prevention
- SOC 2 Type II - CSP provides evidence of implemented security controls for audit requirements
Organizations working with regulated industries or enterprise clients find CSP compliance necessary for contract approval.
4. Alignment with Evolving Browser Security Models
Modern browsers are progressively deprecating unsafe-inline and unsafe-eval
directives. Chrome, Firefox, and Safari roadmaps indicate stricter enforcement of separation between
code and data. CSP-compliant frontends remain compatible with upcoming browser security enhancements
rather than requiring emergency refactoring when browsers enforce breaking changes.
Future-proofing: Google's "Trusted Types" API and other browser-native XSS defenses work optimally with existing CSP implementations.
5. Cleaner and More Maintainable Frontend Architecture
CSP enforcement drives structured JavaScript practices - no inline event handlers, no string-to-code evaluation, no scattered script tags throughout templates. This constraint produces:
- Modular component architecture with clear data flow
- Reduced technical debt from legacy inline code patterns
- Easier debugging through centralized script sources
- Better code review processes with explicit script dependencies
Teams report improved onboarding time for new developers working with CSP-compliant codebases due to enforced architectural consistency.
CSP Implementation Challenges
Achieving CSP compliance requires rebuilding how frontend code works. For Hyva theme extensions, this means adapting the Alpine.js framework to work within strict security rules.
Main Challenges
Moving JavaScript logic from template files into separate, organized modules
Restructuring how buttons and interactive elements respond to user actions
Ensuring all scripts work properly with Hyva's security verification system
Extracting code that was embedded directly in page templates
The development work is substantial - CSP implementation typically requires rewriting 60-80% of the frontend integration. The same functionality must work correctly both with strict security enabled and in standard Hyva setups.
MageMe Security Approach
Security is foundational to our development process, not a compliance checkbox. Every MageMe product undergoes continuous XSS vulnerability testing throughout its lifecycle, with identified issues addressed in accelerated release cycles.
routeCSP Compliance Roadmap
- EasyQuote - CSP-compliant as of Hyva compatibility module 1.4 (current release)
- WebForms - CSP implementation in active development
- HidePrice Pro - Scheduled for CSP refactoring following WebForms completion
This phased approach ensures thorough testing and refinement of our CSP implementation methodology with each product release, allowing us to apply learned improvements to subsequent extensions.
EasyQuote CSP Implementation: Complete Hyva Module Refactoring
Achieving CSP compliance for EasyQuote required rebuilding the Hyva compatibility module from the ground up. We restructured the entire frontend architecture to meet Alpine.js and Hyva security standards.
What We Did
Moved JavaScript code into proper external modules following Hyva best practices
Removed all code patterns that triggered CSP warnings
Every feature works identically with enhanced security
Works seamlessly whether you have strict CSP enabled or not
verifiedQuality Assurance
The refactored module underwent extensive testing across:
- Multiple security policy configurations
- Various Hyva theme versions (1.3.x and 1.4.x)
- Different Magento 2.4.x releases
- Integration scenarios with other Hyva-compatible extensions
This comprehensive rebuild provides the secure foundation your store needs for long-term success.
Upgrade to EasyQuote Hyva Module 1.4
The CSP-compliant Hyva compatibility module is available now for all EasyQuote license holders. Access version 1.4 through your MageMe account dashboard.
Related EasyQuote Features
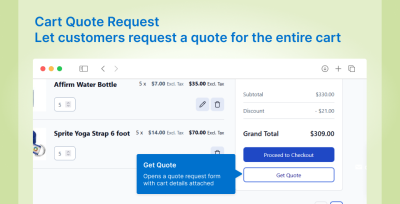
Explore capabilities that make EasyQuote the comprehensive B2B solution
Quick Checkout Links
One-click conversion from quote approval to completed checkout with pre-populated customer data
Tier Pricing System
Volume-based pricing with multiple quantity tiers in single quotes for wholesale operations
Complete Shipping Integration
Full address, method, and cost handling with automatic order conversion
Drag-and-Drop Item Ordering
Visual quote item organization that persists across PDF exports and customer views
Key Takeaways
- Zero CSP violations — all inline scripts removed and replaced with CSP-safe external modules and event listeners.
- First CSP-compliant quote extension — EasyQuote is the first Magento 2 quote management module to pass strict CSP validation on Hyvä.
- Full Hyvä integration — native Alpine.js components and Tailwind CSS classes instead of jQuery/KnockoutJS dependencies.
- Security hardening — CSP compliance protects against XSS attacks and code injection by enforcing script source policies.
- No functionality trade-offs — all EasyQuote features work identically under strict CSP headers.
Frequently Asked Questions
Content Security Policy is a browser security standard that blocks untrusted script execution at the browser level, preventing cross-site scripting (XSS) attacks. CSP enforces strict source allowlisting to mitigate risks from compromised third-party scripts, malicious browser extensions, and injected code targeting payment flows or customer data.
Hyva Theme 1.4, including CSP functionality, became free and open-source in November 2025. Previously requiring a €1,000 license, this change removed the primary barrier to CSP adoption for thousands of merchants running Magento 2 storefronts. CSP-ready architecture is now available to all merchants, not just enterprise clients.
Yes, the CSP-compliant Hyva compatibility module functions identically on stores with or without CSP policies enabled. Existing implementations can upgrade without modifications — CSP protection activates automatically when appropriate policies are configured.
CSP directly supports PCI DSS 4.0 (Requirement 6.4.3 addresses script integrity), GDPR Article 32 (appropriate technical measures for data protection), and SOC 2 Type II (evidence of implemented security controls). Organizations working with regulated industries find CSP compliance necessary for contract approval.
CSP implementation typically requires rewriting 60-80% of frontend integration. Main challenges include component restructuring (moving JavaScript from templates into separate modules), event handling changes, security token integration with Hyva's verification system, and template separation (extracting embedded code).
MageMe is systematically implementing CSP compliance across its entire product portfolio: EasyQuote is CSP-compliant as of Hyva compatibility module 1.4 (current release), WebForms CSP implementation is in active development, and HidePrice Pro is scheduled for CSP refactoring following WebForms completion.